
Pair Programming: Definition, Benefits, and Best Practices
This article provides a comprehensive overview of pair programming, defining the practice and exploring its core roles and techniques. Delving into th...
Discover the latest insights, tutorials and expert analysis on cloud computing, serverless architecture and modern technology solutions.
Stay updated with the latest trends and insights in cloud computing technology

This article provides a comprehensive overview of pair programming, defining the practice and exploring its core roles and techniques. Delving into th...
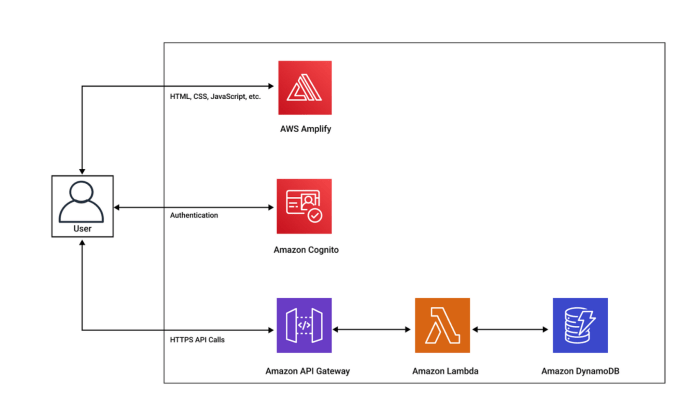
Serverless architectures necessitate innovative state management strategies, and DynamoDB provides a powerful solution. This article explores how to l...
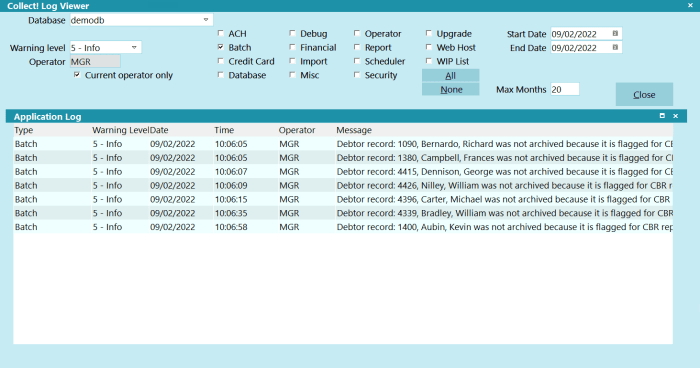
Data archival for retired applications is crucial for maintaining compliance, leveraging historical insights, and mitigating risk. This comprehensive...
This comprehensive article explores Knative, a powerful open-source platform designed to bring serverless capabilities to Kubernetes. From its core co...

In the modern digital environment, maintaining uninterrupted access to online services is crucial. This article explores the vital role of load balanc...

In today's dynamic digital environment, choosing the right security strategy is critical. This article differentiates between proactive and reactive s...
Protecting your cloud data requires a well-defined backup strategy. This comprehensive guide offers a step-by-step approach to designing a robust back...
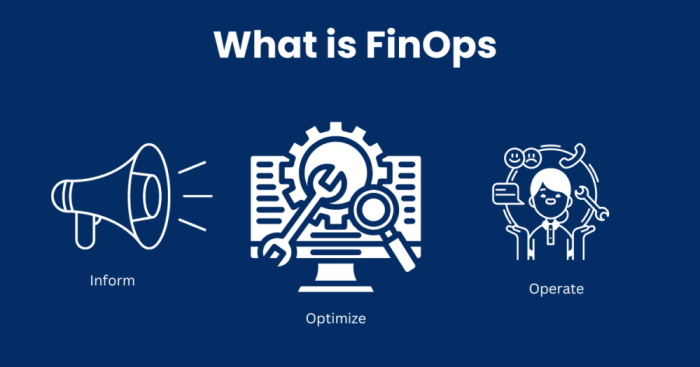
This article outlines a strategic approach to establishing a FinOps culture, essential for optimizing cloud spending and achieving financial disciplin...
This comprehensive guide provides a detailed roadmap for creating effective cloud architecture diagrams, from foundational concepts to advanced techni...
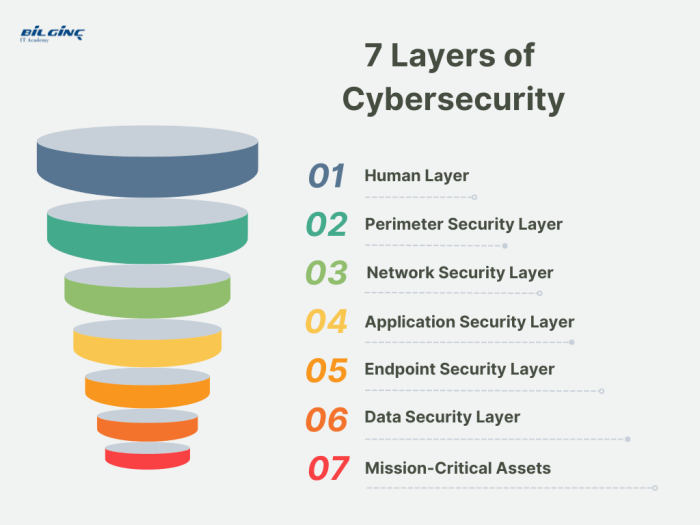
The principle of defense in depth is a critical cybersecurity strategy that employs a layered approach to security, recognizing the vulnerability of a...

This comprehensive guide delves into the world of Configuration Management Databases (CMDBs), exploring their core functionalities, diverse types, and...
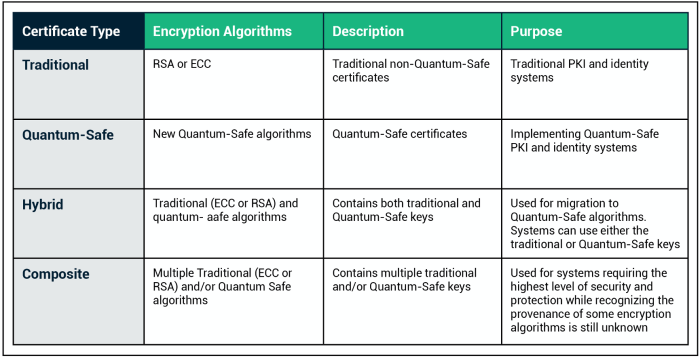
Delve into the fascinating world of quantum cryptography, a revolutionary approach to securing digital information. This article explores the fundamen...